T33n Leak Online: Child Exploitation Concerns and What You Need to Know
 Daniel Santos
Daniel Santos 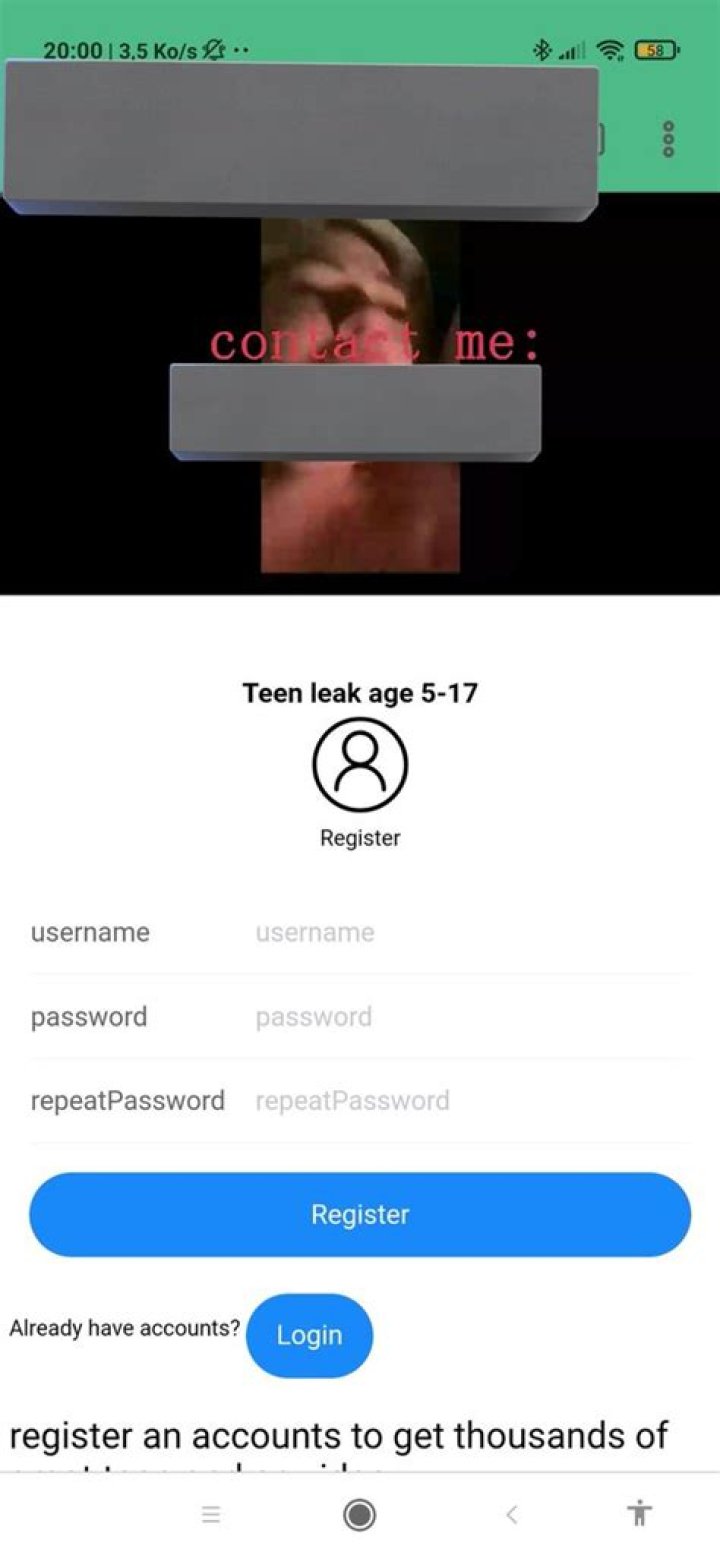
Let’s talk about something heavy but super important—T33n leak online and the alarming rise of child exploitation on the internet. If you haven’t heard about it yet, buckle up, because this is a topic that affects us all, whether we’re parents, guardians, or just concerned citizens. The internet has revolutionized the way we live, work, and communicate, but with great power comes great responsibility. And unfortunately, some people out there aren’t using that power for good.
We’re living in an age where technology connects us like never before. From social media platforms to gaming apps, kids these days have access to a world of possibilities at their fingertips. But with those possibilities come risks—big ones. The recent T33n leak online has sparked global outrage, highlighting how vulnerable young people can be when it comes to online safety.
Now, I know what you’re thinking: “What exactly is a T33n leak?” and “How does this relate to child exploitation?” Don’t worry, we’ll dive deep into all of that. But first, let’s set the stage. This isn’t just about one incident; it’s about a growing trend that demands our attention. If we don’t act now, the consequences could be devastating.
So, why are we talking about this? Because knowledge is power. Understanding the problem is the first step toward solving it. Whether you’re a parent trying to keep your kids safe, a teacher educating students about digital citizenship, or simply someone who cares about the well-being of children, this article is for you. Let’s break it down together.
What Exactly Is a T33n Leak?
Alright, let’s start with the basics. A T33n leak refers to the unauthorized sharing of personal information, images, or videos involving teenagers—often minors—on the internet. In many cases, these leaks involve sensitive content that can lead to exploitation, bullying, and even legal issues. It’s not just a random thing happening here and there; it’s a widespread issue that’s gaining traction in the wrong way.
Here’s the kicker: most of the time, these leaks happen without the consent of the individuals involved. Think about it—how would you feel if someone shared your private photos or messages without your permission? It’s not just embarrassing; it’s traumatic. And when it happens to kids, the impact can last a lifetime.
Let’s break it down even further:
- T33n leaks often occur on social media platforms, forums, or dark web marketplaces.
- The content shared can range from innocent selfies to more explicit material.
- In some cases, hackers or malicious actors exploit vulnerabilities in apps or websites to gain access to private data.
How Does It Happen?
Now, you might be wondering how these leaks even happen in the first place. Well, there are several ways:
- Phishing Attacks: Scammers trick teens into giving away their passwords or personal information.
- Hacked Accounts: Weak passwords or outdated security settings make it easy for hackers to breach accounts.
- Sextortion: Some predators manipulate teens into sending explicit content, then threaten to release it unless they get what they want.
It’s a scary thought, but it’s happening more often than you’d think. And the worst part? Many victims don’t even realize they’ve been targeted until it’s too late.
The Alarming Rise of Child Exploitation Online
Child exploitation online isn’t a new phenomenon, but it’s definitely on the rise. According to a report by the National Center for Missing & Exploited Children (NCMEC), there were over 21 million reports of child exploitation in 2022 alone. That’s a staggering number, and it’s only increasing as more kids spend time online.
Let’s talk about the numbers for a sec:
- More than 50% of teenagers admit to sharing personal information with strangers online.
- Approximately 20% of teens have received unwanted sexual solicitations.
- One in five children aged 10-17 has been exposed to unwanted pornography online.
These stats are alarming, to say the least. But they also highlight the urgent need for action. We can’t afford to ignore this issue any longer. It’s time to take a stand and protect our kids from the dangers lurking in cyberspace.
Who’s Behind These Exploitations?
So, who are the bad guys here? It’s not always some shadowy figure lurking in the dark corners of the internet. Sometimes, it’s people we know and trust—friends, classmates, or even family members. Other times, it’s organized criminal networks operating on a global scale.
Here’s the breakdown:
- Pedophiles and Predators: Individuals who seek out and exploit children for sexual purposes.
- Cyberbullies: Kids or adults who use the internet to harass, intimidate, or humiliate others.
- Scammers and Hackers: People who exploit vulnerabilities in technology to steal data or manipulate victims.
The bottom line? No matter who’s behind it, child exploitation is a violation of trust and a violation of human rights. And it’s our responsibility to stop it.
Why Is This Such a Big Deal?
You might be thinking, “Why is this such a huge issue? Can’t we just ignore it and move on?” The answer is a resounding NO. Here’s why:
First of all, the psychological impact on victims can be devastating. Imagine being a teenager and having your private moments exposed to the world. The shame, the embarrassment, the fear—it’s enough to make anyone want to crawl into a hole and disappear. And let’s not forget the long-term effects—depression, anxiety, and even PTSD are all too common among victims of online exploitation.
Secondly, there’s the legal aspect. In many countries, distributing or possessing child exploitation material is a serious crime. And if you’re caught, the consequences can be life-altering. Not to mention the social stigma that comes with being labeled as someone involved in such activities.
Lastly, there’s the societal impact. When we allow child exploitation to thrive, we’re sending a message that it’s okay to treat people—especially children—as objects. And that’s not the kind of world we want to live in.
What Are the Long-Term Effects?
The effects of child exploitation can last a lifetime. Victims often struggle with:
- Low self-esteem
- Trust issues
- Difficulty forming healthy relationships
- Substance abuse
- Suicidal thoughts
It’s not just about the immediate aftermath; it’s about the lasting damage that can affect every aspect of a person’s life. That’s why prevention and support are so crucial.
How Can We Stop It?
Okay, so now that we’ve talked about the problem, let’s talk about the solution. Here are a few things we can do to combat child exploitation online:
1. Educate Yourself and Others
Knowledge is power, and the more we know, the better equipped we are to protect ourselves and our loved ones. Teach kids about online safety, privacy settings, and the importance of not sharing personal information with strangers.
2. Use Technology Wisely
There are plenty of tools out there designed to help parents monitor their kids’ online activity. From parental controls to tracking apps, these resources can make a big difference in keeping kids safe.
3. Report Suspicious Activity
If you see something, say something. Whether it’s a suspicious message or a concerning post, report it to the appropriate authorities. Every little bit helps.
4. Support the Victims
Victims of child exploitation need our support more than ever. Offer a listening ear, a helping hand, or even just a kind word. Let them know they’re not alone and that there’s hope for a brighter future.
Real-Life Stories: The Human Side of T33n Leaks
Let’s put a face to the issue. Here are a few real-life stories that illustrate the impact of T33n leaks and child exploitation:
Case Study 1: Sarah’s Story
Sarah was a typical 15-year-old girl who loved taking selfies and sharing them on social media. One day, she received a message from someone claiming to have private photos of her that she never intended to share. They threatened to post them unless she sent them more explicit content. Scared and confused, Sarah didn’t know what to do. Thankfully, her parents found out and reported the incident to the authorities. While Sarah is now receiving counseling and support, the experience left a lasting impact on her life.
Case Study 2: James’ Story
James, a 13-year-old boy, fell victim to a phishing scam after clicking on a link in a suspicious email. The hacker gained access to his social media accounts and began posting inappropriate content under his name. It took weeks for James and his family to regain control of his accounts and repair the damage. The incident taught him a valuable lesson about online security, but the emotional toll was significant.
Legal Implications and What You Need to Know
When it comes to T33n leaks and child exploitation, the law is on our side—at least to some extent. Here’s what you need to know:
In many countries, distributing or possessing child exploitation material is a criminal offense. Penalties can include hefty fines, jail time, and even being placed on a sex offender registry. And if you’re a victim, you have legal rights too. You can report the incident to law enforcement, seek legal counsel, and even pursue civil action against the perpetrators.
But here’s the thing: the law can only do so much. It’s up to us as individuals, communities, and societies to create a safer online environment for everyone, especially our kids.
What Can You Do If You’re a Victim?
If you or someone you know has been a victim of a T33n leak or child exploitation, here’s what you can do:
- Report the incident to local law enforcement or a trusted authority.
- Seek support from friends, family, or mental health professionals.
- Take steps to secure your online accounts and protect your personal information.
Looking Ahead: The Future of Online Safety
As technology continues to evolve, so too must our efforts to keep kids safe online. The good news is that there are plenty of organizations, activists, and tech companies working hard to make the internet a safer place. From developing better security features to raising awareness about online safety, progress is being made.
But we can’t rely solely on others to do the work. It’s up to each and every one of us to take responsibility for our own safety and the safety of those around us. Whether it’s educating ourselves, supporting victims, or advocating for change, we all have a role to play.
What’s Next?
The future of online safety depends on collaboration, innovation, and a shared commitment to protecting our most vulnerable populations. By working together, we can create a world where kids can explore the internet without fear of exploitation or harm.
Conclusion: Taking Action Today
Let’s recap what we’ve learned today:
- T33n leaks and child exploitation are serious issues affecting millions of kids worldwide.
- The psychological, legal, and societal impacts are significant and far-reaching.
- There are steps we can take to prevent exploitation and support victims.
- Education, technology, and advocacy are key to creating a safer online environment.
So, what can you do right now? Start by educating yourself and others about online safety. Use the resources available to you, and don’t hesitate to report suspicious activity. Most importantly, show compassion and support to those who have been affected by this issue.
Together, we can make a difference. Let’s not wait for someone else to take the lead. The time to act is now.



