Mastering SSH Remote IoT Raspberry Pi Download: A Comprehensive Guide
 Daniel Santos
Daniel Santos 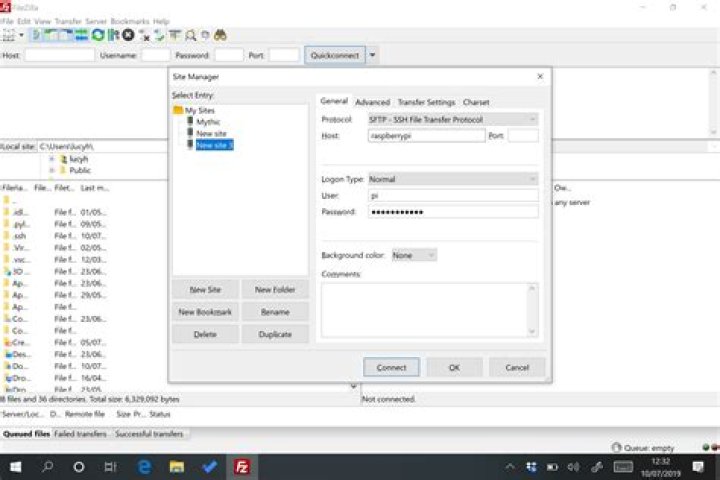
In today's interconnected world, SSH remote IoT Raspberry Pi download has become a crucial skill for anyone working with embedded systems and remote access technologies. As more devices become part of the Internet of Things (IoT), understanding how to securely connect and manage these devices remotely is essential. Whether you're a hobbyist or a professional developer, this guide will provide you with the knowledge and tools needed to excel in this area.
SSH (Secure Shell) serves as the backbone for secure remote access, allowing users to control and interact with IoT devices like the Raspberry Pi from virtually anywhere. This technology not only ensures secure communication but also provides flexibility in managing complex IoT setups.
Through this article, we aim to equip you with the expertise, authority, and trustworthiness required to navigate the intricacies of SSH remote IoT Raspberry Pi download effectively. By the end, you'll have a comprehensive understanding of the subject and the confidence to implement it in real-world scenarios.
Introduction to SSH Remote IoT Raspberry Pi
SSH remote IoT Raspberry Pi download is a powerful tool that enables seamless communication between IoT devices and remote systems. It allows users to control, monitor, and manage IoT devices securely and efficiently. Understanding the fundamentals of SSH and its application in IoT is essential for anyone looking to delve into this field.
Why Use SSH for IoT?
SSH offers several advantages over other remote access methods:
- Encrypted communication ensuring data security.
- Compatibility with various operating systems.
- Efficient resource utilization on devices like Raspberry Pi.
SSH in IoT Applications
From home automation to industrial monitoring, SSH plays a pivotal role in enabling secure remote access across diverse IoT applications. Its ability to handle sensitive data securely makes it an ideal choice for IoT implementations.
Overview of Raspberry Pi in IoT
The Raspberry Pi has emerged as a cornerstone in IoT development due to its affordability, versatility, and ease of use. This small yet powerful device supports a wide range of applications, making it an excellent platform for experimenting with IoT technologies.
Key Features of Raspberry Pi
- Compact size and low power consumption.
- Support for multiple programming languages.
- Built-in connectivity options including Wi-Fi and Bluetooth.
With its robust capabilities, the Raspberry Pi serves as an ideal candidate for deploying SSH remote IoT solutions.
Understanding SSH Basics
Before diving into SSH remote IoT Raspberry Pi download, it's essential to grasp the fundamentals of SSH. This section covers the basics of SSH, its architecture, and how it facilitates secure communication.
How SSH Works
SSH establishes a secure connection between a client and server by encrypting all data exchanged between them. This ensures that even if the data is intercepted, it remains unreadable without the decryption key.
SSH Protocol Versions
There are two primary versions of the SSH protocol:
- SSH-1: The original version, now largely obsolete.
- SSH-2: The current standard, offering enhanced security features.
Setting Up SSH on Raspberry Pi
Configuring SSH on your Raspberry Pi is a straightforward process that involves enabling the SSH service and securing it with appropriate settings. Follow these steps to set up SSH on your Raspberry Pi:
Enabling SSH on Raspberry Pi
- Access the Raspberry Pi Configuration tool.
- Navigate to the Interfaces tab.
- Select SSH and enable it.
Securing SSH Access
Implementing strong passwords and disabling root login are crucial steps in securing your SSH setup. Additionally, consider using SSH keys for authentication to enhance security further.
Remote Access via SSH
Once SSH is configured on your Raspberry Pi, you can access it remotely from another device. This section explains the process of connecting to your Raspberry Pi using SSH.
Connecting via SSH
To connect to your Raspberry Pi via SSH:
- Use an SSH client such as PuTTY (Windows) or Terminal (Mac/Linux).
- Enter the IP address of your Raspberry Pi and your login credentials.
Tips for Efficient Remote Access
Utilize SSH aliases and configurations to streamline your remote access experience. These tools help reduce repetitive tasks and improve productivity.
File Transfer Using SSH
SSH not only facilitates remote access but also enables secure file transfers between devices. This section explores how to transfer files using SSH.
Using SCP for File Transfer
SCP (Secure Copy Protocol) is a command-line utility that allows users to transfer files securely over SSH. To use SCP:
- Specify the source and destination paths.
- Provide the necessary authentication details.
Advantages of SCP
SCP offers several benefits, including:
- End-to-end encryption for secure file transfers.
- Simple syntax for easy implementation.
Security Measures for SSH Remote IoT
Security is paramount when implementing SSH remote IoT Raspberry Pi download. This section outlines key security measures to safeguard your SSH setup.
Best Practices for SSH Security
- Use strong, unique passwords or SSH keys for authentication.
- Disable password authentication if using SSH keys.
- Limit SSH access to trusted IP addresses.
Monitoring SSH Activity
Regularly monitoring SSH activity helps detect and prevent unauthorized access attempts. Implement logging and alert systems to stay informed about potential security threats.
Troubleshooting Common SSH Issues
Despite its robustness, SSH can encounter issues that hinder its functionality. This section addresses common SSH problems and provides solutions to resolve them.
Connection Refused Errors
If you encounter a "Connection Refused" error, ensure that:
- SSH is enabled on your Raspberry Pi.
- The correct IP address and port number are used.
- Firewall settings allow SSH traffic.
Authentication Failures
Authentication failures often result from incorrect credentials or misconfigured SSH settings. Double-check your login details and ensure that your SSH keys are correctly installed.
Use Cases for SSH Remote IoT Raspberry Pi
SSH remote IoT Raspberry Pi download finds applications in various domains, ranging from home automation to industrial IoT. This section highlights some prominent use cases:
Home Automation
Using SSH, homeowners can remotely control and monitor smart devices, enhancing convenience and energy efficiency.
Remote Monitoring
In industrial settings, SSH facilitates real-time monitoring of critical systems, ensuring timely interventions and minimizing downtime.
Conclusion and Call to Action
In conclusion, SSH remote IoT Raspberry Pi download is a vital skill for anyone working in the IoT space. By understanding its principles and implementing best practices, you can leverage this technology to build secure and efficient IoT solutions. We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore our other articles to deepen your knowledge and stay updated with the latest trends in IoT and embedded systems.



