How to Use RemoteIoT Behind Firewall Using Mac Server Example
 Michael Henderson
Michael Henderson 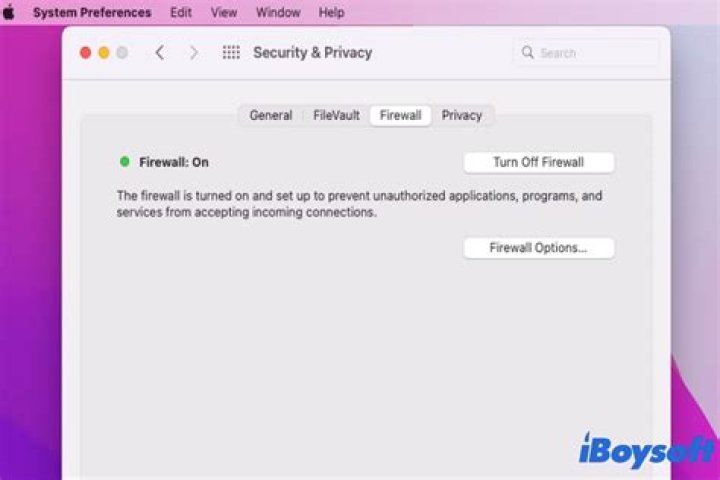
Managing IoT devices remotely while maintaining security is a common challenge for businesses and developers. One solution is using a Mac server to route RemoteIoT traffic behind a firewall. This setup allows secure access to IoT devices without compromising network integrity. In this article, we'll explore how to configure and use RemoteIoT behind a firewall using a Mac server example, ensuring seamless connectivity while adhering to security best practices.
As IoT adoption grows, so does the need for secure and efficient management of connected devices. A firewall acts as a critical barrier, protecting internal networks from unauthorized access. However, this protection can sometimes hinder the functionality of IoT devices. By leveraging a Mac server, businesses can create a secure bridge that allows RemoteIoT to operate seamlessly within a protected environment.
This article is designed for IT professionals, developers, and network administrators who need to implement secure IoT solutions. We'll cover everything from the basics of RemoteIoT and firewalls to advanced configuration steps, ensuring you have a comprehensive understanding of the process.
Introduction to RemoteIoT and Firewalls
Understanding RemoteIoT
RemoteIoT is a powerful tool that enables remote management of IoT devices. It allows users to monitor, control, and interact with devices from anywhere in the world. Whether you're managing smart home devices, industrial sensors, or agricultural equipment, RemoteIoT simplifies the process by providing a centralized platform for device management.
The Role of Firewalls
A firewall is a security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier between a trusted internal network and untrusted external networks, such as the internet. Firewalls are essential for protecting sensitive data and preventing unauthorized access to network resources.
However, firewalls can sometimes block legitimate traffic, including RemoteIoT communications. This is where the need for a secure bridge, such as a Mac server, comes into play.
Benefits of Using a Mac Server
A Mac server offers several advantages when it comes to managing RemoteIoT behind a firewall:
- Security: Mac servers are known for their robust security features, making them ideal for handling sensitive IoT data.
- Stability: macOS is built on a stable UNIX foundation, ensuring reliable performance even under heavy loads.
- Compatibility: Mac servers can seamlessly integrate with a wide range of IoT devices and third-party applications.
- Ease of Use: macOS provides an intuitive interface, making it easy for administrators to configure and manage the server.
Overview of the Setup Process
Setting up RemoteIoT behind a firewall using a Mac server involves several key steps:
- Prepare the Mac server by installing necessary software and configurations.
- Configure the firewall to allow RemoteIoT traffic while maintaining security.
- Install and configure RemoteIoT on the Mac server.
- Adjust network settings to ensure proper communication between devices.
- Implement additional security measures to protect against potential threats.
This process requires careful planning and execution to ensure a secure and functional setup.
Configuring the Firewall
Identifying Required Ports
Before configuring the firewall, it's essential to identify the ports used by RemoteIoT. Common ports include:
- HTTP: Port 80
- HTTPS: Port 443
- SSH: Port 22
- Custom IoT Ports: Varies based on device configuration
Ensure these ports are open in the firewall to allow RemoteIoT traffic.
Setting Up Firewall Rules
Firewall rules should be configured to allow only necessary traffic. Use the following guidelines:
- Allow incoming traffic on specified ports for RemoteIoT.
- Block all other incoming traffic to prevent unauthorized access.
- Enable outbound traffic for device communication.
Regularly review and update firewall rules to adapt to changing security requirements.
Installing RemoteIoT on Mac Server
Installing RemoteIoT on a Mac server involves the following steps:
- Download the RemoteIoT software from the official website.
- Install the software on the Mac server, following the provided instructions.
- Configure the software to connect to your IoT devices.
- Test the connection to ensure proper functionality.
Refer to the official documentation for detailed installation instructions and troubleshooting tips.
Adjusting Network Settings
Configuring IP Addresses
Ensure that the Mac server has a static IP address to maintain consistent connectivity. Use the following steps:
- Open System Preferences on the Mac server.
- Select Network and choose the active network interface.
- Set the IP address, subnet mask, and router details manually.
Setting Up DNS
Configure DNS settings to resolve domain names for RemoteIoT communication. Use a reliable DNS provider to ensure fast and accurate resolution.
Implementing Security Measures
Using SSL/TLS Encryption
Encrypt RemoteIoT traffic using SSL/TLS to protect data in transit. Obtain a valid SSL certificate from a trusted provider and install it on the Mac server.
Enabling Two-Factor Authentication
Enhance security by enabling two-factor authentication for RemoteIoT access. This adds an extra layer of protection, ensuring only authorized users can access the system.
Troubleshooting Common Issues
Common issues when setting up RemoteIoT behind a firewall include:
- Connection Failures: Verify that all required ports are open in the firewall.
- Slow Performance: Optimize network settings and ensure adequate server resources.
- Security Alerts: Regularly update software and firewall rules to address potential threats.
Consult the RemoteIoT documentation and community forums for additional troubleshooting tips.
Optimizing RemoteIoT Performance
Optimizing RemoteIoT performance involves:
- Regularly updating software and firmware to ensure compatibility and security.
- Monitoring network traffic to identify and resolve bottlenecks.
- Implementing load balancing for high-traffic environments.
These steps will help ensure a smooth and efficient RemoteIoT experience.
Conclusion and Next Steps
In conclusion, using a Mac server to manage RemoteIoT behind a firewall is an effective way to ensure secure and reliable IoT device management. By following the steps outlined in this article, you can create a robust setup that meets your business needs while maintaining network security.
We encourage you to:
- Leave a comment below with your thoughts or questions about this article.
- Share this article with others who may find it useful.
- Explore additional resources and tutorials on our website for more information on IoT and network security.
Stay informed and keep your IoT systems secure!
For further reading, refer to the following sources:



